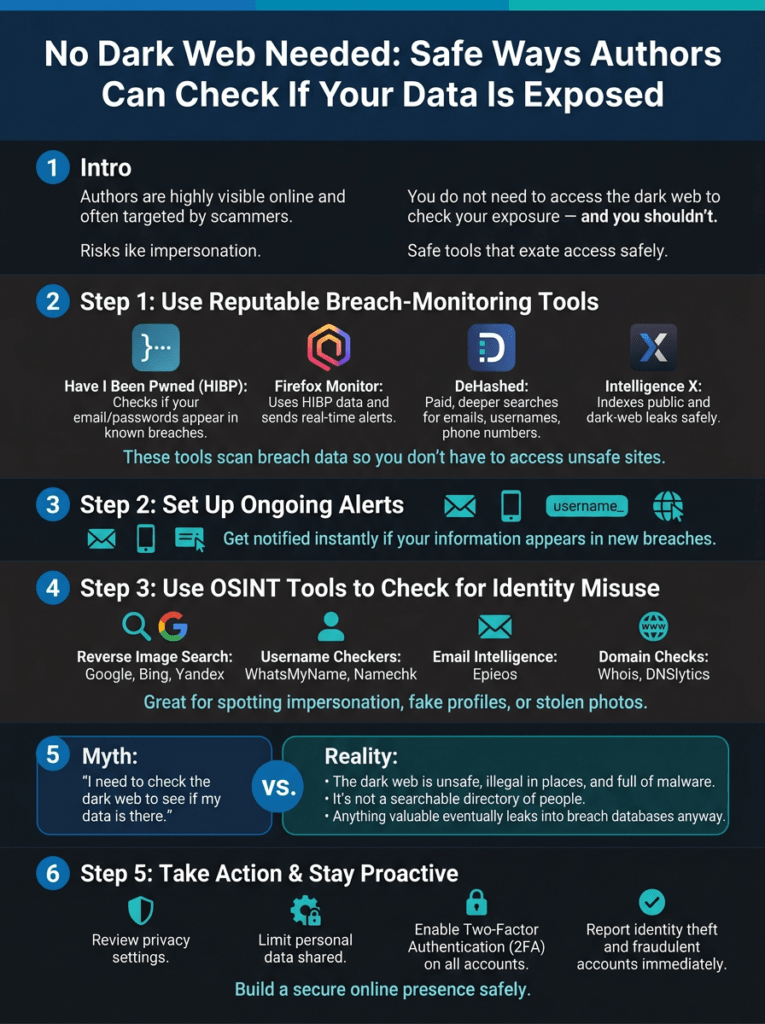
No Dark Web Needed: Safe Ways Authors Can Check If Your Data Is Exposed

As authors, we’re no strangers to the digital world—pouring our creativity into manuscripts, building online platforms, and connecting with readers across social media and newsletters. But that visibility comes with risks. Scammers love targeting writers, stealing emails, usernames, and personal details to impersonate us, phish fans, or peddle fake books. It’s natural to wonder: Has my information leaked somewhere shady, like the dark web? The good news? You don’t need to venture into that dangerous territory to find out. In fact, you shouldn’t. There are safe, legal, and highly effective alternatives used by cybersecurity pros, journalists, and fraud investigators every day.
Professionals rarely “browse” the dark web themselves—it’s risky, often illegal for certain content, and riddled with malware. Instead, they rely on breach-monitoring tools and open-source intelligence (OSINT) methods that pull the same leaked data to the surface without exposing you to harm. Here’s your step-by-step guide to checking your exposure like an expert, minus the danger.
- Start with Reputable Breach-Monitoring Tools
These services scan massive databases of known data breaches—including those that end up traded on the dark web—without you ever needing to go there. Enter your email, phone number , or username, and they’ll tell you if it’s surfaced in leaks.
- Have I Been Pwned (HIBP): The gold standard. Free and trusted worldwide, it checks if your email or passwords appear in thousands of breaches. Pro tip: Use it with a password manager to avoid reusing compromised credentials.
- Firefox Monitor: Powered by HIBP’s database, it adds real-time alerts for new breaches. Sign up once, and it watches your inboxes passively.
- DeHashed: A paid tool favored by investigators. It digs deeper into emails, usernames, phone numbers, and even hashed passwords from dark web dumps.
- Intelligence X: Indexes public and dark web leaks safely, letting you search without direct access.
These tools are battle-tested and updated constantly as new breaches emerge. Authors like you can use them to spot if your reader list signup data or publisher-shared info has leaked.
- Set Up Ongoing Breach Alerts
Why check once when you can monitor forever? Alerts notify you instantly if your details pop up in fresh leaks—mimicking dark web surveillance without the sketchiness.
Configure watches for:
- Your primary and secondary emails
- Phone numbers tied to your author profiles
- Usernames across platforms (e.g., your pen name on Twitter/X or Goodreads)
- Custom domains (like your website or book landing pages)
Services like Firefox Monitor, HIBP, and DeHashed offer this for free or at a low cost. For authors, it’s a gamechanger: Imagine getting pinged the moment a scammer’s breach includes your fan database.
- Leverage OSINT Tools for Identity Misuse
Scammers don’t just steal data—they impersonate. OSINT tools help you scan the clear web for signs of theft, like fake profiles or stolen photos.
- Reverse image search: Upload your author headshot to Google Images, Bing, or Yandex. Spot it on scam sites or bogus Amazon author pages in seconds.
- Username checks: Tools like WhatsMyName or Namechk scan 100+ sites for your handle’s reuse—perfect for catching copycat accounts on Instagram or TikTok.
- Email intel: Epieos reveals where your email appears online, flagging suspicious registrations.
- Domain sleuthing: Whois or DNSlytics checks if scammers registered knockoff domains mimicking yours (e.g., yournamebooks.com).
These are free, fast, and author-friendly. I’ve used them to uncover impersonators hawking “my” books to unsuspecting readers.
- Demystify the Dark Web: Why You Don’t Need It
Understanding what’s actually on the dark web sets realistic expectations—and keeps you safe.
It’s not a magical “people search” directory. You’ll find:
- Raw stolen data dumps from breaches
- Criminal marketplaces for IDs and credit cards
- Hacker forums
- Malware kits
- Illegal services
No casual browsing here: It’s malware-infested, legally dicey (accessing some content can flag you to authorities), and proximity to criminals is a bad idea. Crucially, anything valuable leaks to the open web eventually, where breach tools index it. Skip the dark web—you’re not missing a thing.
- Targeted Checks for Author-Specific Threats
If your concern is identity theft or scammers exploiting your author name, here are targeted, safe checks tailored to writers. To spot fake accounts mimicking you, scour platforms like Facebook, LinkedIn, and writing communities such as Absolute Write, then cross-reference with scam-watch groups like Reddit’s r/Scams.
For emails popping up in suspicious places, combine breach-monitoring tools with Epieos for deeper intel. Reverse image search is your best friend against photo theft, quickly exposing deepfakes or hijacked profile pics.
Finally, hunt for your name in scams by Googling “[your name] scam” alongside databases like the BBB Scam Tracker or Authors Against Scammers reports—all without stepping into danger.
Take Action Today: Protect Your Author Brand
Data breaches happen—Writers Beware reports scam attempts spiking yearly. But with these tools, you reclaim control without fear. Start with HIBP today, set alerts, and run an OSINT sweep. If you spot trouble, report it: Freeze credits, notify platforms, and share on Authors Against Scammers to warn others.
Stay vigilant, not paranoid. Your words are your power—don’t let scammers steal your story.
Post inspired by cybersecurity best practices. Tools linked are free unless noted. Always use unique passwords and 2FA.
Rae Stonehouse is a Canadian author, publisher, and advocate committed to exposing publishing scams and supporting writers through education and community. As the creator of Authors Against Scammers, Rae provides clear, practical guidance to help writers protect their work, their money, and their peace of mind. His books and resources reflect a lifelong dedication to empowering others through knowledge, clarity, and real‑world experience.



0 Comments